


Security engineer focused on vulnerability management and application security. Build the tooling, the dashboards, the triage workflows, and the risk models that turn a pile of scanner output into something teams actually act on. Also find the bugs myself. 120+ on HackerOne and counting.



Build and run vulnerability management programs for enterprise clients. The full pipeline: intake from SAST, DAST, SCA, pentests, and bug bounty. Finding correlation, risk scoring, SLA enforcement, remediation tracking, and reporting that actually reaches different audiences in a way they understand.
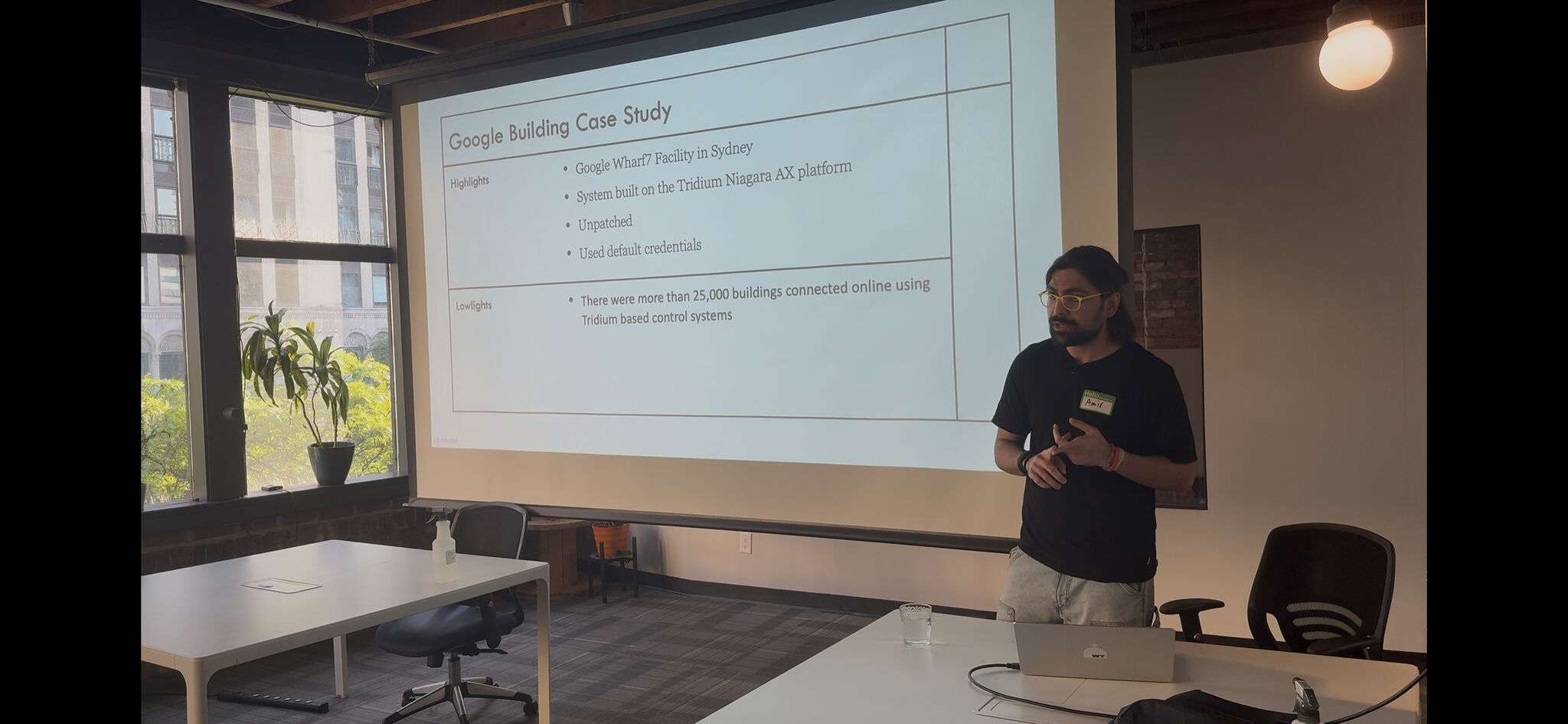
Also do the hands on work. Pentesting, security code review, vulnerability research. 120+ validated findings on HackerOne against companies like PayPal, Sony, AT&T, and Airbnb. Most of those are multi step attack chains, not scanner output.
The thing that ties it together is tooling. Write production tools in Python, Go, and Rust that automate the boring parts of vulnerability management so the team can focus on the findings that actually matter. Dashboards for engineering, leadership, and compliance. Triage automation that routes to the right team with the right context.
Scanners produce a lot of noise. Pull from every source, deduplicate, enrich with asset context and severity, then prioritize. One finding, one owner, one SLA.
Fixing individual vulnerabilities one at a time is a losing game. Find the root cause, work with the dev team to eliminate the entire category. That is how the backlog actually shrinks.
Engineering needs technical detail and fix guidance. Leadership needs trend lines and risk posture. Compliance needs control mapping. Same data, different view. Build all three.
Languages: Python, Go, Rust, JavaScript, Bash, SQL
Security: Burp Suite Pro, Nuclei, Semgrep, CodeQL, SAST/DAST, SCA
Vuln Mgmt: Finding correlation, risk scoring, SLA models, Jira integration, dashboard development
Compliance: SOC 2, ISO 27001, PCI DSS
If you need someone who finds vulnerabilities and builds the program that manages them, get in touch.